
Email Hosting and Protection
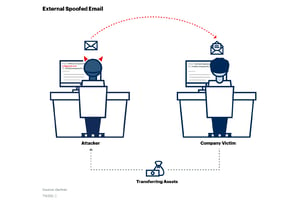
Protect your organization from Business Email Compromise with next-generation email security powered by Twinstate Technologies.
Protect yourself from the #1 attack vector; email.
100% Cloud-Based
Our cloud-based Hosted Exchange server provides all of the key features you would expect from email, alongside basic spam and virus filtering, and limited email encryption capabilities.
Email Archival & Encryption
Our Email Archival service provides scalable, in-the-cloud email retention and storage, securely pulling messages from the server. It stores them in the cloud using 256-bit encryption, the same Advanced Encryption Standard (AES) used to protect top secret information.
Attachment & URL Inspection
Our approach to email protection aims to block phishing, sophisticated malware, and spam well before reaching and breaching your network. We guard against the latest cyber dangers with click-time link scanning, advanced anti-malware, and gray/bulk mail filtering.
How It Works
All-in-One Email Security
Email protection scans incoming emails, rejects them if they are 100% malicious, and flags any emails that look suspicious. Our email protection solution even includes user awareness training, so if you click on a link in an email, it will bring you to a browser and ask you, "is this link/attachment safe," helping to increase your awareness on potentially malicious links.
PRODUCT FEATURE TWO
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy eirmod tempor invidunt ut labore et dolore magna aliquyam erat, sed diam voluptua. Lorem ipsum dolor sit amet.
After three months, 33% of training users report they've changed something in their daily lives to make them more secure
MimecastLondon, United Kingdom
Email Hosting and Protection
Pain Points Solved
- Communication resiliency
- Our cloud-delivered solution has integrated continuity, meaning email is always available to end-users on Outlook, mobile, PC and Mac
- Scanned and secured messaging
- Never send out sensitive information unencrypted again. Secure messaging inspects every message to ensure that sensitive information is encrypted and never sent out in a readable cleartext format.
- Malicious content filtering and link inspection
- Stop malicious emails that contain harmful attachments, misleading URLs, impersonation attempts, fraud, and business email compromises from ever reaching your network.
Let's Get Started